Issue
After installing a self-signed certificate via Internet explorer as detail in article SSL Certificates - Security Certificate Risk warning logging in to WorkStation or WebStation using H...
There is still a warning in Chrome and Firefox that the site is "Not secure"
This warning is not seen in the earlier versions of Internet Explorer but from version 11 it is also seen in Internet Explorer.
Product Line
EcoStruxure Building Operation
Environment
WebStation
Cause
Different browsers have different policies to Self-signed Certificates and display a different warning, but still use HTTPS.
These policies may change over time, but it is not something that can be controlled
Without a neutral and recognized third party—such as a certificate authority—verifying certificate ownership, a certificate is meaningless.
To better understand, when doing something like creating an HTTPS connection you have the following chain:
A client web browser making the request to the server.
The remote web server sending data back to the client.
And an HTTPS certificate authorized by a neutral 3rd party that vouches that the server is who it is and the encryption is valid because of that.
A self-signed certificate is inherently untrusted because anyone can generate a self-signed certificate. Anyone including an entity that deliberately pretends to be something/someone they aren’t. With a self-signed certificate there is simply no trusted third party that has the basic human procedures set to simply state, “Okay, this domain has a certificate we issued them and thus you can trust them. We say they are in fact the domain the claim to be and not an imposter.”
And since anyone in the world can create a self-signed certificate on their own, it’s usage has inherent trust issues. What makes a certificate valid has very little to do with deep technology or encryption techniques but what makes it valid is a process centered around a neutral—and recognized—third party validating a usage procedure and browser makers adhering to respect of those procedures.
At the end of the day, an encryption key pair is an utterly meaningless pile of bits and bytes without the enforcement of the processes and procedures that surround them.
Resolution
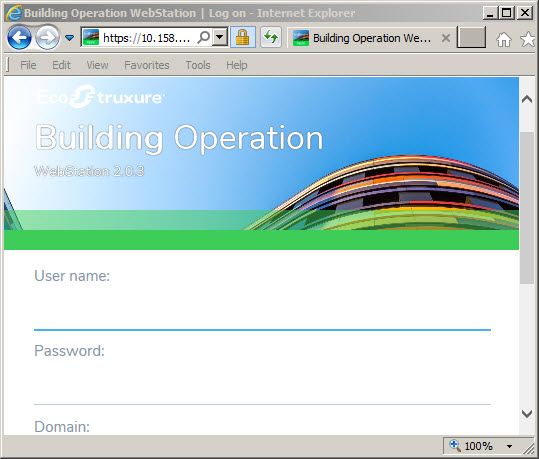
Internet Explorer - No warning
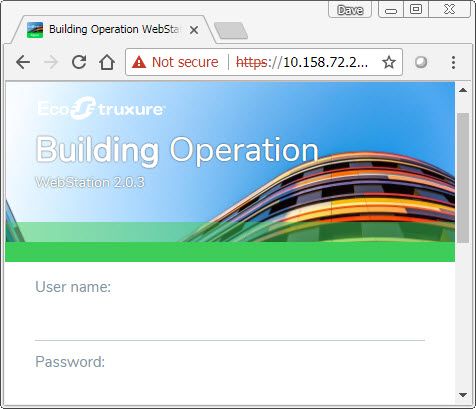
Chrome - "Not Secure" shown
Firefox - Initially a "Your connection is not secure" warning is seen
"10.158.7xx.xxx:xxx uses an invalid security certificate.
The certificate is not trusted because it is self-signed.
Error code: MOZILLA_PKIX_ERROR_SELF_SIGNED_CERT"
Add Exception, allows access as below
The best way to permanently remove the warning is to pay for a certificate from a certificate authority. See this forum post on how to get generate and add a certificate from a certificate authority